Complete Features to Meet WebOps needs
Kelebihan yang menjadi pilihan populer untuk mengelola web hosting
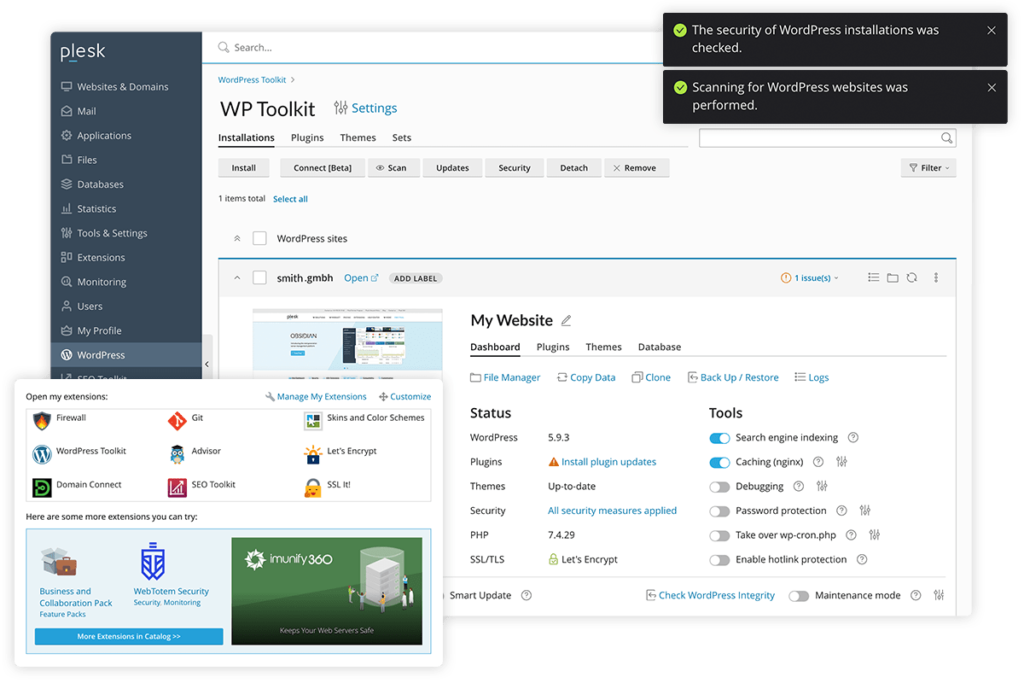
Extension
More than 100+ Extensions available in Plesk. Do more with your platform when you integrate tools such as DigiCert SSL, CloudLinux, Cloudflare, Sitejet Builder, NodeJs, PHP, NGINX, Let's Encrypt, Git, ImunifyAV, Backup, and many more.
Website Builder
Create a fast, responsive, and SEO-friendly website that users and search engines will love. Choose a template, customize it with the drag & drop editor, and hit ‘publish’ to go live.
Web Hosting Business
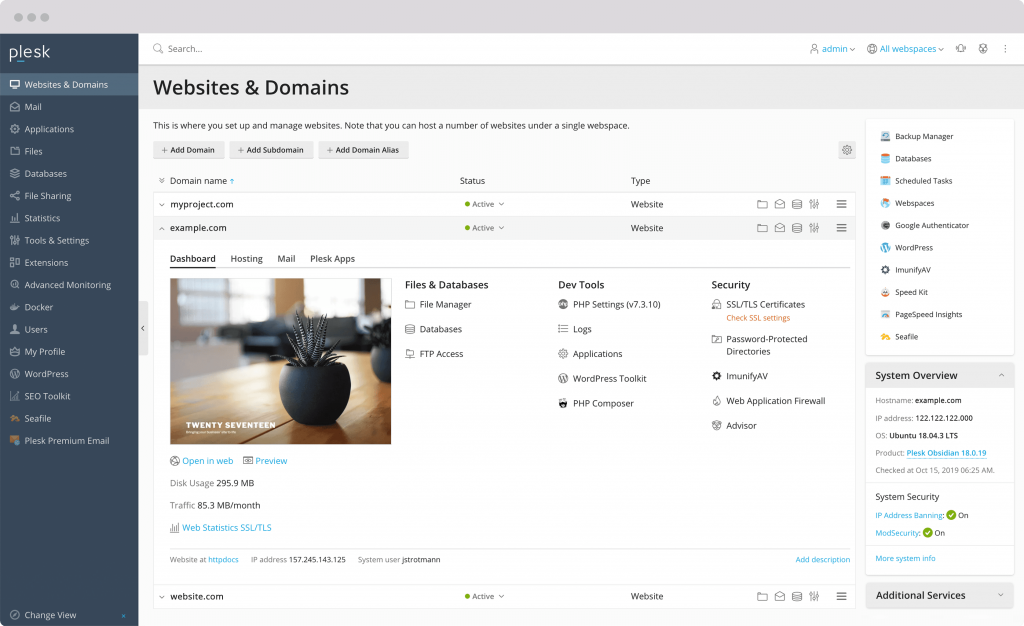
Set up easily and offer web hosting solutions to customers. Web-based control panel components offer simplicity for end users and flexibility for developers and content creators. Manage hosting services, websites, email, and all other services from a single control panel that is intuitive, attractive, and easy to use.
Manage Server Plesk
Enjoy the benefits of using Plesk Control Panel with full support from our team.
|
Scope of Work The following is the scope of Plesk server installation and management services that we will perform. Please note that each installation requires a license, and we can also perform additional installations upon request. |
|||||
|---|---|---|---|---|---|
| Instalasi & Konfigurasi | |||||
| Web Server | Apache, NGINX, LiteSpeed | ||||
| Programming Language | PHP, PHP Selector, Node.js, Ruby, .NET Toolkit | ||||
| Application | WordPress, Laravel, Joomla, Docker, Git, Sitejet Builder, dan 20+ apps lainnya | ||||
| Sistem Operasi | AlmaLinux, Rocky Linux, CloudLinux | ||||
| Cache | Memcached, Redis | ||||
| Antivirus & WAF | ModSecurity, Imunify360, KernelCare, cPGuard, Bitninja | ||||
| Backup Management | |||||
| Third-Party Integration | CSF Plugins, WHMCS, Softaculous | ||||
| DNS Cluster | |||||
| Hardening | |||||
| Server/Hosting Migration | 5 Website / 5 Domain | ||||
| Email Deliverability | SPF, DKIM, DMARC, rDNS/PTR, Relay Email | ||||
| Performance Tuning | |||||
| Monitoring | Uptime & Incident Report | ||||
| Custom Request | |||||
| Delivery | After the order is received or within a maximum of 1x24 hours | ||||
Frequently Asked Questions and Technical Questions
See frequently asked questions
1. Reputation: The reputation of the email sender is very important. If the sender has a good reputation, the emails they send are more likely to reach the recipient's inbox.
2. Server Configuration: The sender's server configuration must be set up correctly, including DNS settings, SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance).
3. Email Content: The content and structure of the email must comply with the guidelines and policies of the email service provider. Emails with relevant and high-quality content are more likely to reach the recipient's inbox.
1. SPF is a protocol that allows domain owners to specify which servers are authorized to send emails on behalf of that domain. With SPF, a DNS record is added to the domain configuration that identifies which servers have permission to send emails from that domain. When an email is sent, the recipient can verify the authenticity of the email by checking the SPF record to ensure that the sending server is legitimate.
2. DKIM is an email authentication method that uses asymmetric cryptography techniques to secure emails from forgery. In DKIM, the sender's domain signs the email using a private key known only to the sender. The recipient can verify the digital signature attached to the email using the public key available in the sender's domain DNS record. If the signature is valid, it indicates that the email has not been altered and originates from a verified domain.
3. DMARC (Domain-based Message Authentication, Reporting, and Conformance): DMARC is a policy framework that combines SPF and DKIM to improve email security. With DMARC, domain owners can define policies to control how emails that fail SPF or DKIM authentication should be handled. In addition, DMARC also provides reports that allow domain owners to track and analyze domain usage, including email spoofing attempts.